When you implement Conditional Access to protect your end-users and the company data there will often be different Conditional Access frameworks for different user types and licenses.
For example you might have production users within your environment, that only needs to be allowed to sign-in from a compliant device from a specific corporate network.
On the other hand you might also have regular office workers around the globe that is using Azure-AD resources from different devices that could be protected through Identity Protection and therefore also use Risk Based Conditional Access framework where each sign-in and user is constantly being evaluated for risks depending on sign-in patterns,application used,what device they are on,the device compliance status,OS,location,browser and so on.
When you have different Conditional Access frameworks for different user types, you often end-up with several different security groups that enables Conditional Access, and also security groups for excluding end-users from Conditional Access policies.
To get the insights of all users that have been actively excluded from Conditional Access is important,the last thing you want is to have users that is persistent excluded and is left unprotected.
To track end-users that have been excluded from Conditional Access, we will use the Identity Governance function, or more precisely the access review functionality.
Before we move on and configure this, be sure to check the examples and requirements below
Examples of how access review will help you tracking excluded Conditional Access users
When we have configured an access review for a specific security group, we will get an automated access review for that security group each week.
This will help us to get insight of all end-users that have been excluded from conditional access, and we will also be able to either allow or deny the users from being excluded in this solution.
Example of how the notification email will look like when its time to review the group:

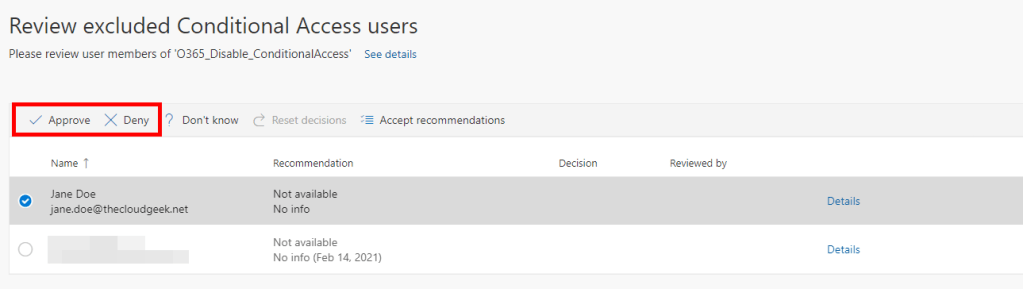
Example of how the access review site looks like when the review is open for change, you could either approve or deny the membership for the specific end-user selected
Requirements for access review
License requirements
Azure AD Premium P2 license is required for each account that is performing one of the following tasks:
- users who are assigned as reviewers
- users who perform a self-review
- users as group owners who perform an access review
- users as application owners who perform an access review
Global Administrators and User Administrators are not requerd to have an Azure AD Premium P2 license as long as they only are:
Create the access reviews
Configurating the access reviews
Apply the descions from the access review
Feeling uncertain about this? Please see some great examples from Microsoft
Configuration of Access Review
Let’s move forward and configure our first access review
1. Sign-in to the Azure-Portal
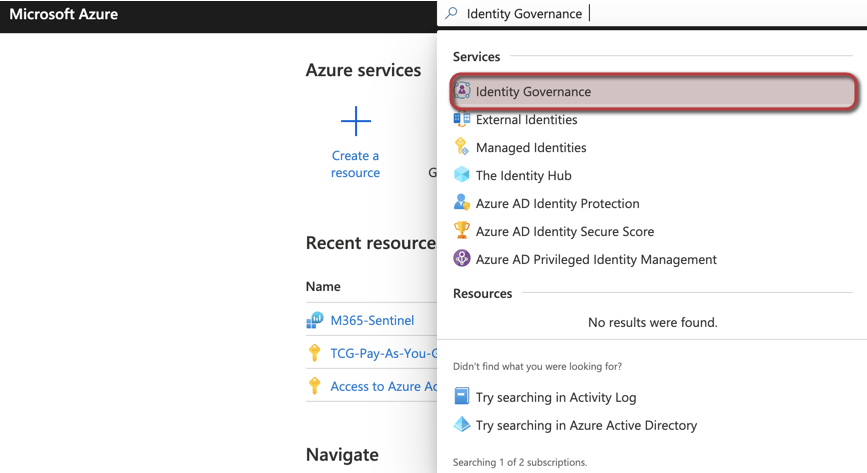
2. Search for Identity Governance
3. Click on Identity Governance
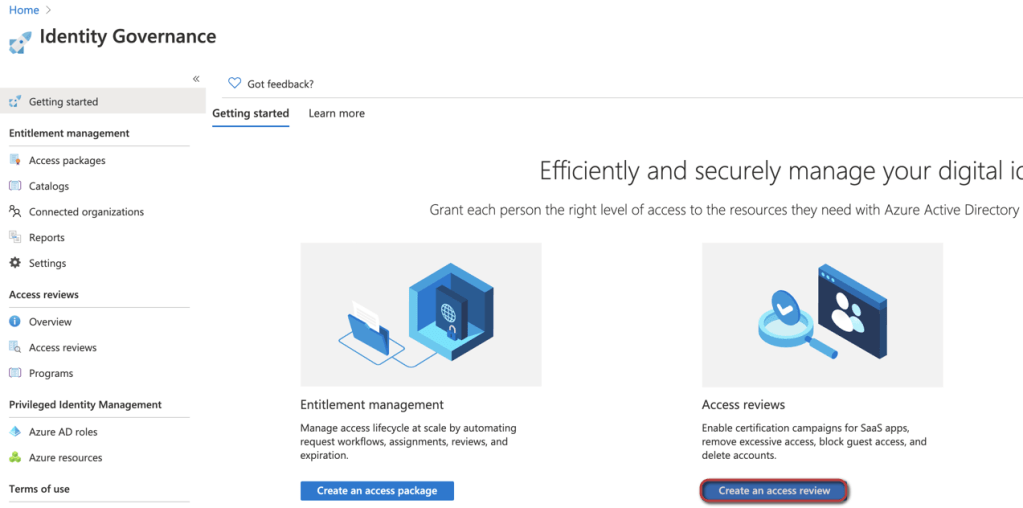
4.Click on Create an access review
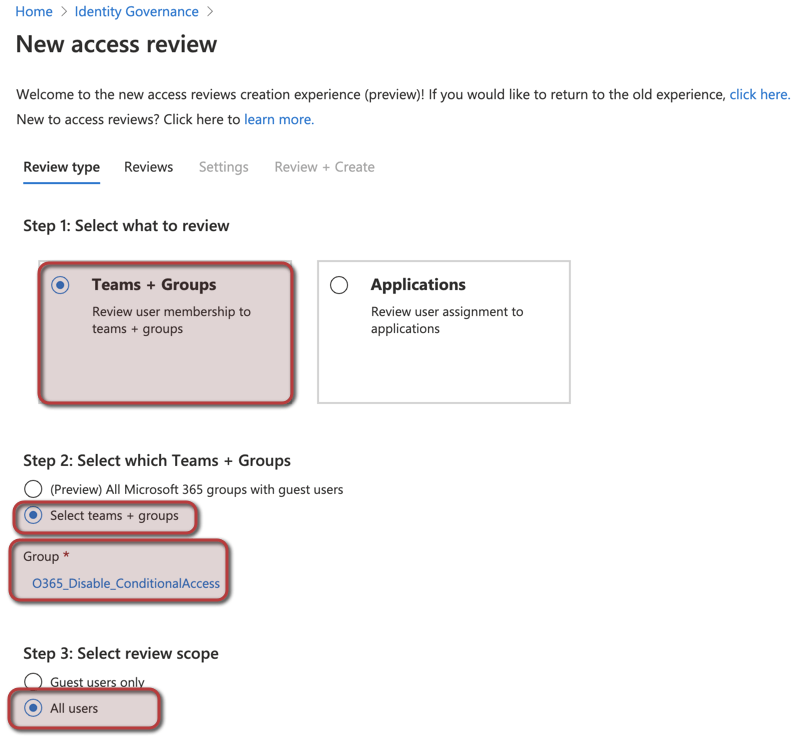
5. Select to review Teams + Groups
6. Select what security group to monitor with access reviews
7. Select to review all users
8. Select the security group or users that will be able to review the membership of the security group “O365_Disable_ConditionalAccess”
9. Select the recurrency of the review, in this example we will choose the review to recur every week, and have the duration of three days.
This means that the reviewers have three days to go through the review and take decisions on the detected users that is excluded from Conditional Access in your tenant.
We will also choose the review to never end, to make sure that we get the insights of excluded users each week.

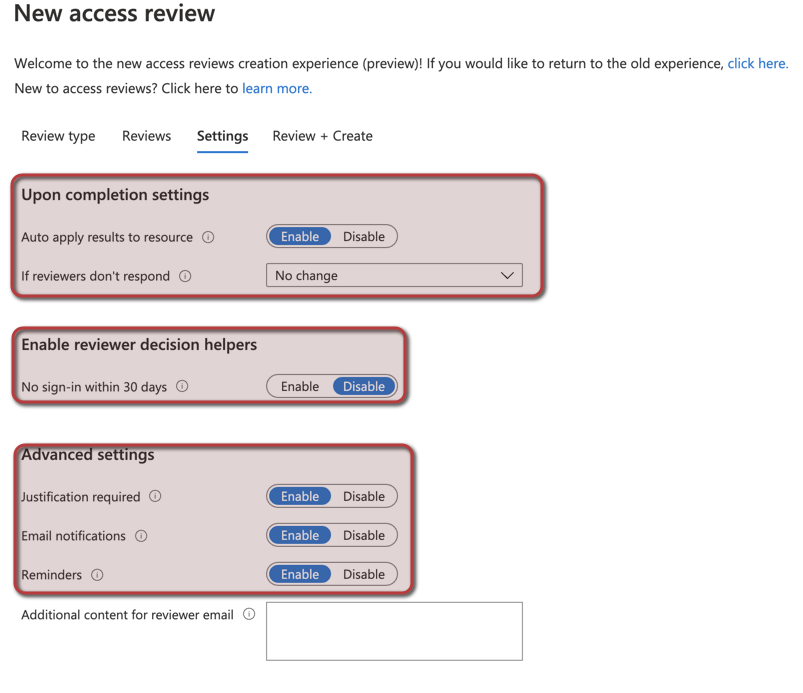
10. Now we will focus on configure the actual settings for the review.
We will enable auto apply result to resource, this will result on based on our review action, the members of the security group we are reviewing will either remain as member or be removed as member.
If an reviewer ignore the access review during the three day window no changes will be made to the security group.
We will disable the decision helper is this scenario,and enable justification,email notifications and the reminders.
11. Name the access review and write an description, and then click on create, you have now created the access review that will track end-users who have been disabled from Conditional Access

The reviewers will now receive emails when the access review is ready, and they will have three days to review the membership of the security group. If the reviewers ignore the access review and simply do not make any changes, nothing will change.
