Not too long ago I where involved in a security incident where the attacker used phishing to gain access to several end-users Microsoft 365 credentials.
In this case, the customer didn’t have MFA or Conditional Access implemented, leaving them exposed for this type of general attack that unfortunately is really common.
To make a long story short, at one point we simply needed an easy way to find all end-users who had registered, updated or deleted their MFA authentication methods.
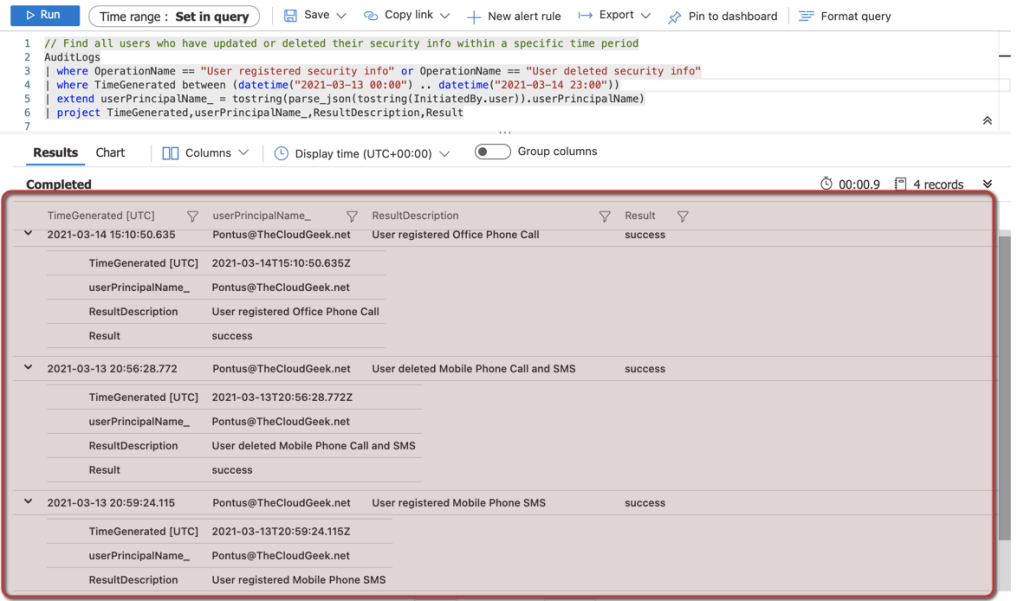
In this case, we had access to the sign-in and audit logs in Azure Monitor and therefor I created a small KQL query
// Find all users who have updated or deleted their security info within a specific time period
AuditLogs
| where OperationName == "User registered security info" or OperationName == "User deleted security info"
| where TimeGenerated between (datetime("2021-XX-XX 00:00") .. datetime("2021-XX-XX 00:00"))
| extend userPrincipalName_ = tostring(parse_json(tostring(InitiatedBy.user)).userPrincipalName)
| project TimeGenerated,userPrincipalName_,ResultDescription,ResultExample output
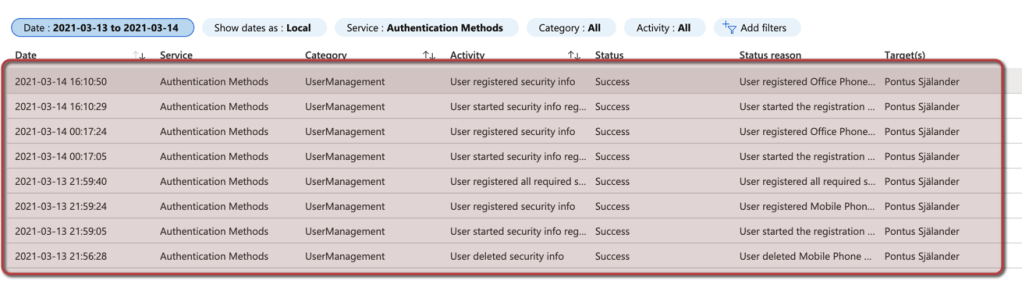
Our logs are not integrated with Azure Monitor or Sentinel, how can we get the same logs?
Depending in the amount of logs, time frame and license it’s still possible for you to get your hands on some of the data at least!
1. Sign-in to the Azure Portal
2. Open Azure Active Directory
3. Open Audit logs
4. Filter on the specific date and time period that is interesting
5. Filter on service = Authentication Method
Example output:
Clear end-users MFA authentication methods
Alright, so we know have some insights in how end-users MFA authentication methods have change during a specific time period. Maybe we find that the attacker have registered new phone numbers, to be able to sign-in if we enforce MFA on the compromised account.
Before i’ll show how you can clear an end-users authentication methods, please be sure to save all information you find on an compromised account. Information as authentication methods could be important in an investigation down the road.
Also, please make sure that you create a framework in the future for how and when end-users can register their MFA authentication methods.
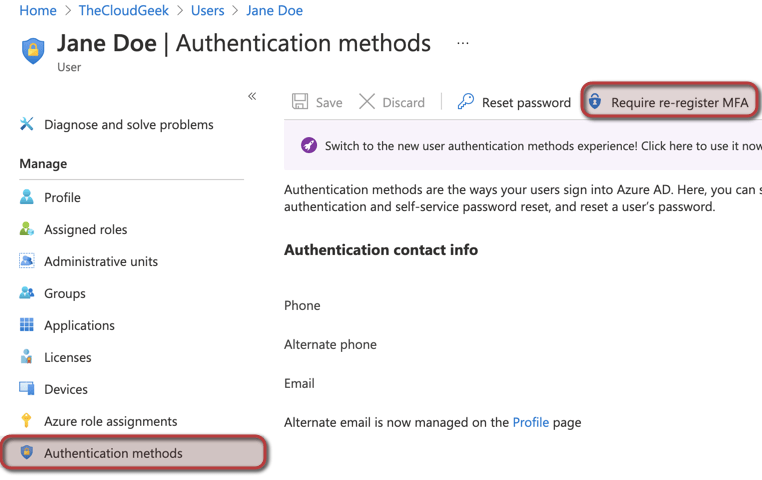
Clear end-users MFA authentication methods through the portal
1. Sign-in to the Azure Portal
2. Open Azure Active Directory
3. Open all users
4. Search for the specific end-user and open the user object
5. Open authentication methods
6. Click on Require re-register MFA
Clear end-users MFA authentication methods through the PowerShell
You can also clear the end-users authentication methods through PowerShell.
For a specific user:
Reset-MsolStrongAuthenticationMethodByUpn -UserPrincipalName user@domain.comFor a group of end-users based on .CSV file
$users = import-csv C:\temp\users.csv -delimiter ","
foreach ($user in $users)
{
$upn=$user.UserPrincipalName
Reset-MsolStrongAuthenticationMethodByUpn -UserPrincipalName $upn
} I hope this can help someone to track down changes in end-users MFA authentication methods 😀